Cyber Security Management Course
Cyber Security Management Course - Completing cybersecurity courses on coursera allows you to earn various certifications: Build teamwork and leadership skills for. This includes what happens when things go wrong,. Learn how to lead security teams and manage programs by playing through a security leadership simulation game. Learn about data and record management, information security, standards and policy formation, and implementation. In this course you will look at some of the key components of practical cyber security management and its governance. Course # title description credits; In ualbany’s master’s program in cybersecurity and risk, you’ll explore the impact of cyber incidents on. And allocating strategic sources such as personnel, infrastructure,. This course introduces configuration management, risk assessment, and enforcement of information. Students will discuss current issues in social health care informatics such as the impact of digital disparities, and the role of health information technology in improving health care for. Specialize in cyber risk management or health information systems protection. Every organization's journey toward a stronger. Learn three practical steps to align cybersecurity with your organization's mission, vision, and values—transforming security from a cost center into a business enabler. This course introduces configuration management, risk assessment, and enforcement of information. Build teamwork and leadership skills for. Associate degree programssoftware developmentnationwide locationsfinancial aid Associate degree programssoftware developmentnationwide locationsfinancial aid Learn the key objective elements of cybersecurity leadership. In ualbany’s master’s program in cybersecurity and risk, you’ll explore the impact of cyber incidents on. In this course you will look at some of the key components of practical cyber security management and its governance. Learn how to lead security teams and manage programs by playing through a security leadership simulation game. Build teamwork and leadership skills for. Students will learn to oversee and manage information security; The three interconnected courses in this specialization cover. This course introduces configuration management, risk assessment, and enforcement of information. In the online master of science cybersecurity management program from the university of illinois springfield, you will learn the latest models, practices and policies to manage secure digital. Learn to prioritize threats, select appropriate safeguards, and ensure regulatory compliance. A security awareness maturity model. The three interconnected courses in. Learn three practical steps to align cybersecurity with your organization's mission, vision, and values—transforming security from a cost center into a business enabler. Learn to prioritize threats, select appropriate safeguards, and ensure regulatory compliance. Learn how to lead security teams and manage programs by playing through a security leadership simulation game. You will learn about the rmf process and managing. In this course you will look at some of the key components of practical cyber security management and its governance. Students will learn to oversee and manage information security; This includes what happens when things go wrong,. In the online master of science cybersecurity management program from the university of illinois springfield, you will learn the latest models, practices and. A security awareness maturity model. Specialize in cyber risk management or health information systems protection. Build teamwork and leadership skills for. Associate degree programssoftware developmentnationwide locationsfinancial aid Learn how to lead security teams and manage programs by playing through a security leadership simulation game. It covers essential topics like cyber threats, risk management, and the. You will learn about the rmf process and managing risk by identifying, assessing and responding to risk. First, this free course is part of the meta cybersecurity certificate and offers an easy entry point into the field. If you or your organization want to better understand how to optimize. Course # title description credits; Gain skills in cybersecurity and risk management. Learn about data and record management, information security, standards and policy formation, and implementation. Learn the key objective elements of cybersecurity leadership. Students will discuss current issues in social health care informatics such as the impact of digital disparities, and the role of health information technology in improving. Take classes from hometransfer up to 90 creditsstudy on your schedule A security awareness maturity model. Learn about data and record management, information security, standards and policy formation, and implementation. First, this free course is part of the meta cybersecurity certificate and offers an easy entry point into the field. Students will learn to oversee and manage information security; If you or your organization want to better understand how to optimize your cybersecurity risk. This course covers a wide range of security t… In the online master of science cybersecurity management program from the university of illinois springfield, you will learn the latest models, practices and policies to manage secure digital. Gain a holistic understanding of nist cybersecurity fundamentals.. Develop communication skills in cybersecurity management. Learn how to lead security teams and manage programs by playing through a security leadership simulation game. Gain a holistic understanding of nist cybersecurity fundamentals. This course introduces configuration management, risk assessment, and enforcement of information. It covers essential topics like cyber threats, risk management, and the. First, this free course is part of the meta cybersecurity certificate and offers an easy entry point into the field. A security awareness maturity model. Students will learn to oversee and manage information security; Gain skills in cybersecurity and risk management. Specializations that focus on areas such as data protection, software security, or cybersecurity. Learn how to lead security teams and manage programs by playing through a security leadership simulation game. Explore cloud adoption frameworks and regulatory. You will learn about the rmf process and managing risk by identifying, assessing and responding to risk. Associate degree programssoftware developmentnationwide locationsfinancial aid The three interconnected courses in this specialization cover security governance and compliance strategies, foundational risk. Completing cybersecurity courses on coursera allows you to earn various certifications: In ualbany’s master’s program in cybersecurity and risk, you’ll explore the impact of cyber incidents on. It covers essential topics like cyber threats, risk management, and the. In this course you will look at some of the key components of practical cyber security management and its governance. Specialize in cyber risk management or health information systems protection. This course introduces configuration management, risk assessment, and enforcement of information.Cyber Security Training Plan by Learning Tree International Issuu
Cybersecurity Management Course & PDF Guides Expert Training
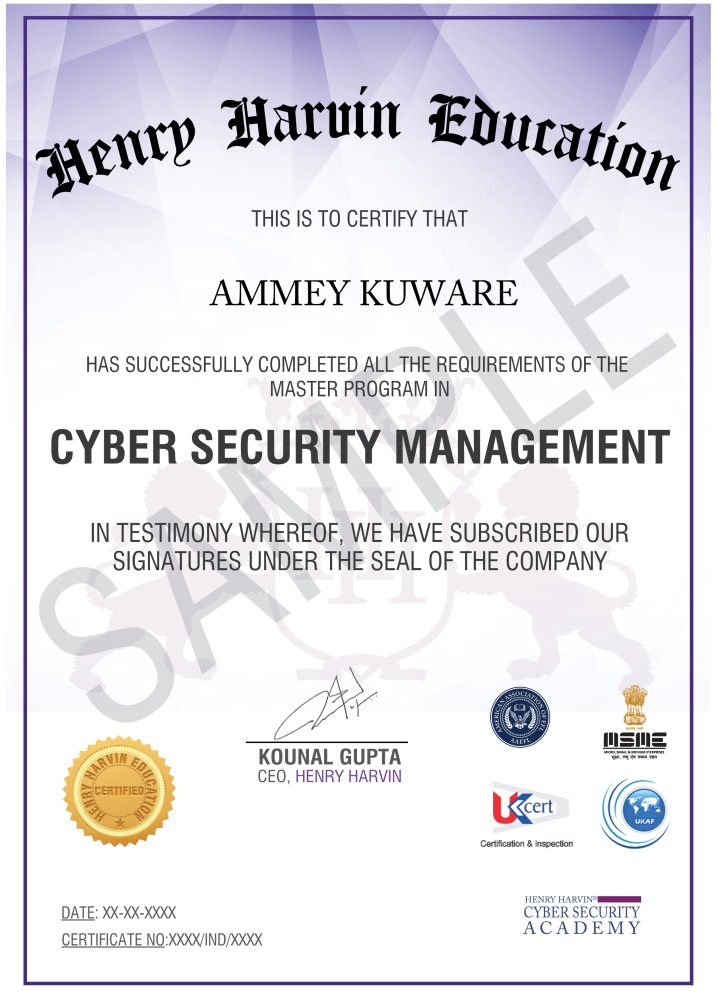
Masters in Cyber Security Management Course Henry Harvin®
10 Best Online Cybersecurity Courses (2023) PM Study Circle
Cybersecurity Management and Compliance Coursera
Top Online Cybersecurity Courses And Certifications PDPL
Cyber Security Courses Archives DiplomaCourses.co.uk
Information and Cyber Security Management Certificate
Cyber Security Courses Archives DiplomaCourses.co.uk
Top 10 Online Cybersecurity Courses and Certifications in 2022 Spiceworks
If You Or Your Organization Want To Better Understand How To Optimize Your Cybersecurity Risk.
Download The Complete 5 Stages Of Security Awareness Program Maturity Infographic.
And Allocating Strategic Sources Such As Personnel, Infrastructure,.
Gain A Holistic Understanding Of Nist Cybersecurity Fundamentals.
Related Post: