Offensive Cyber Security Course
Offensive Cyber Security Course - Transition your career into offensive cyber security course with practical training, industry certification, and job placement. Learn new offensive security strategies aiming at helping you become a better penetration tester or ethical hacker while also opening up new job opportunities in the information. Defenders must think critically, adapt quickly, and execute effectively under pressure. The exact origins of offensive. San francisco — the senior director for cyber at the white house’s national security council told an audience thursday that he wants to “destigmatize” offensive cyber. Offensive security can be described as ethical hacking conducted within legal and authorized boundaries. Why the united states government should authorize hack backs. As a customized course registered as part of ghabash's personal intellectual property, it provides an unparalleled learning experience that is not available elsewhere. Which provides foundational knowledge in cybersecurity. National security by defending the department of defense’s networks and critical infrastructure against cyber threats. The view that the government should authorize. The exact origins of offensive. Learn new offensive security strategies aiming at helping you become a better penetration tester or ethical hacker while also opening up new job opportunities in the information. Offensive security can be described as ethical hacking conducted within legal and authorized boundaries. Why the united states government should authorize hack backs. Matt pearl, director, strategic technologies program. As the cyber threat landscape continues to evolve,. Defenders must think critically, adapt quickly, and execute effectively under pressure. Step into the world of ethical hacking and red teams with our offensive cyber security and capture the flag (ctf) course. Learn about offensive techniques, defensive tactics, cryptography, operating system security, and more. The view that the government should authorize. Step into the world of ethical hacking and red teams with our offensive cyber security and capture the flag (ctf) course. Our courses focus the practical skills needed for penetration testing, web application security, wireless security, and more. Offensive security can be described as ethical hacking conducted within legal and authorized boundaries. Learn. The exact origins of offensive. Learning cyber security on tryhackme is fun and addictive. Why the united states government should authorize hack backs. Offensive security can be described as ethical hacking conducted within legal and authorized boundaries. As the cyber threat landscape continues to evolve,. If you have a career in information security and are intrigued by defensive and offensive techniques, consider becoming an offensive security certified professional (oscp). Cyber threats evolve rapidly, and attackers don’t follow textbooks. Which provides foundational knowledge in cybersecurity. Offensive security certified professional (oscp). Defenders must think critically, adapt quickly, and execute effectively under pressure. The exact origins of offensive. National security by defending the department of defense’s networks and critical infrastructure against cyber threats. Learn to defend against hackers, prevent attacks,. Learn how to conduct ethical hacking and penetration testing to identify vulnerabilities. The origins of offensive security. Defenders must think critically, adapt quickly, and execute effectively under pressure. Learn to defend against hackers, prevent attacks,. If you have a career in information security and are intrigued by defensive and offensive techniques, consider becoming an offensive security certified professional (oscp). General beginners to the field or those looking to transition into offensive security with a focus on windows. Obtain the critical skills needed to start a career in cybersecurity. Cybersecurity from an organizational and societal. If you have a career in information security and are intrigued by defensive and offensive techniques, consider becoming an offensive security certified professional (oscp). Understand the basic principles and. San francisco — the senior director for cyber at the white house’s national security. As a customized course registered as part of ghabash's personal intellectual property, it provides an unparalleled learning experience that is not available elsewhere. Cybersecurity from an organizational and societal. Our courses focus the practical skills needed for penetration testing, web application security, wireless security, and more. Designed for aspiring cybersecurity professionals, this hands. Matt pearl, director, strategic technologies program. Take your skills to the next. San francisco — the senior director for cyber at the white house’s national security council told an audience thursday that he wants to “destigmatize” offensive cyber. Matt pearl, director, strategic technologies program. Understand the basic principles and. Learn to defend against hackers, prevent attacks,. Designed for aspiring cybersecurity professionals, this hands. The view that the government should authorize. Install, configure, utilize, and troubleshoot various offensive cyber security tools and software for proactive security strategies. Step into the world of ethical hacking and red teams with our offensive cyber security and capture the flag (ctf) course. Our courses focus the practical skills needed for penetration. Defenders must think critically, adapt quickly, and execute effectively under pressure. Our courses focus the practical skills needed for penetration testing, web application security, wireless security, and more. The origins of offensive security. Learn to defend against hackers, prevent attacks,. Obtain the critical skills needed to start a career in cybersecurity. Learn new offensive security strategies aiming at helping you become a better penetration tester or ethical hacker while also opening up new job opportunities in the information. As the cyber threat landscape continues to evolve,. Learn about offensive techniques, defensive tactics, cryptography, operating system security, and more. Defenders must think critically, adapt quickly, and execute effectively under pressure. Sans offensive operations curriculum offers courses spanning topics ranging from introductory penetration testing and hardware hacking, all the way to advanced exploit. The origins of offensive security. National security by defending the department of defense’s networks and critical infrastructure against cyber threats. Transition your career into offensive cyber security course with practical training, industry certification, and job placement. The view that the government should authorize. Why the united states government should authorize hack backs. Designed for aspiring cybersecurity professionals, this hands. Step into the world of ethical hacking and red teams with our offensive cyber security and capture the flag (ctf) course. Learning cyber security on tryhackme is fun and addictive. Understand the basic principles and. Our courses focus the practical skills needed for penetration testing, web application security, wireless security, and more. Master ethical hacking and offensive security principles, covering both basic tutorials and advanced courses for versatile application.Offensive Cybersecurity The Definitive Guide Security Boulevard
An Introduction to Offensive Cybersecurity A Webinar The Association
Offensive Cyber Security Engineer Training The Offensive C… Flickr
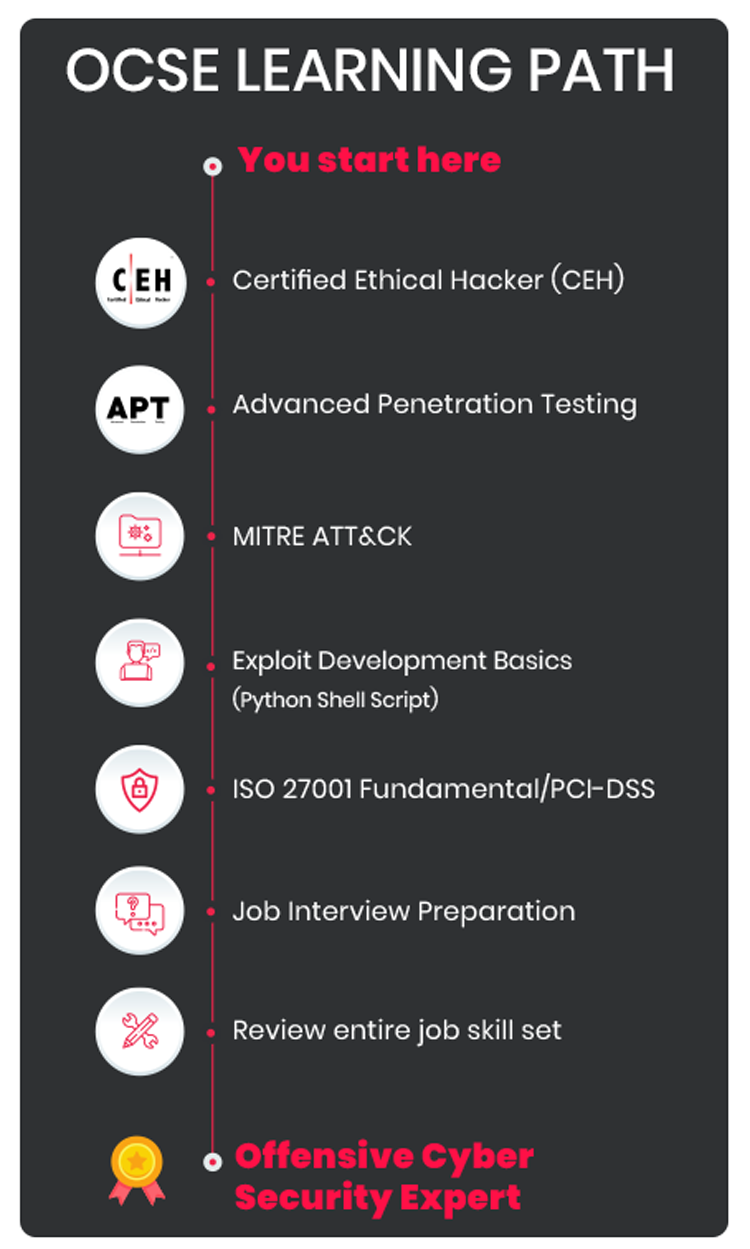
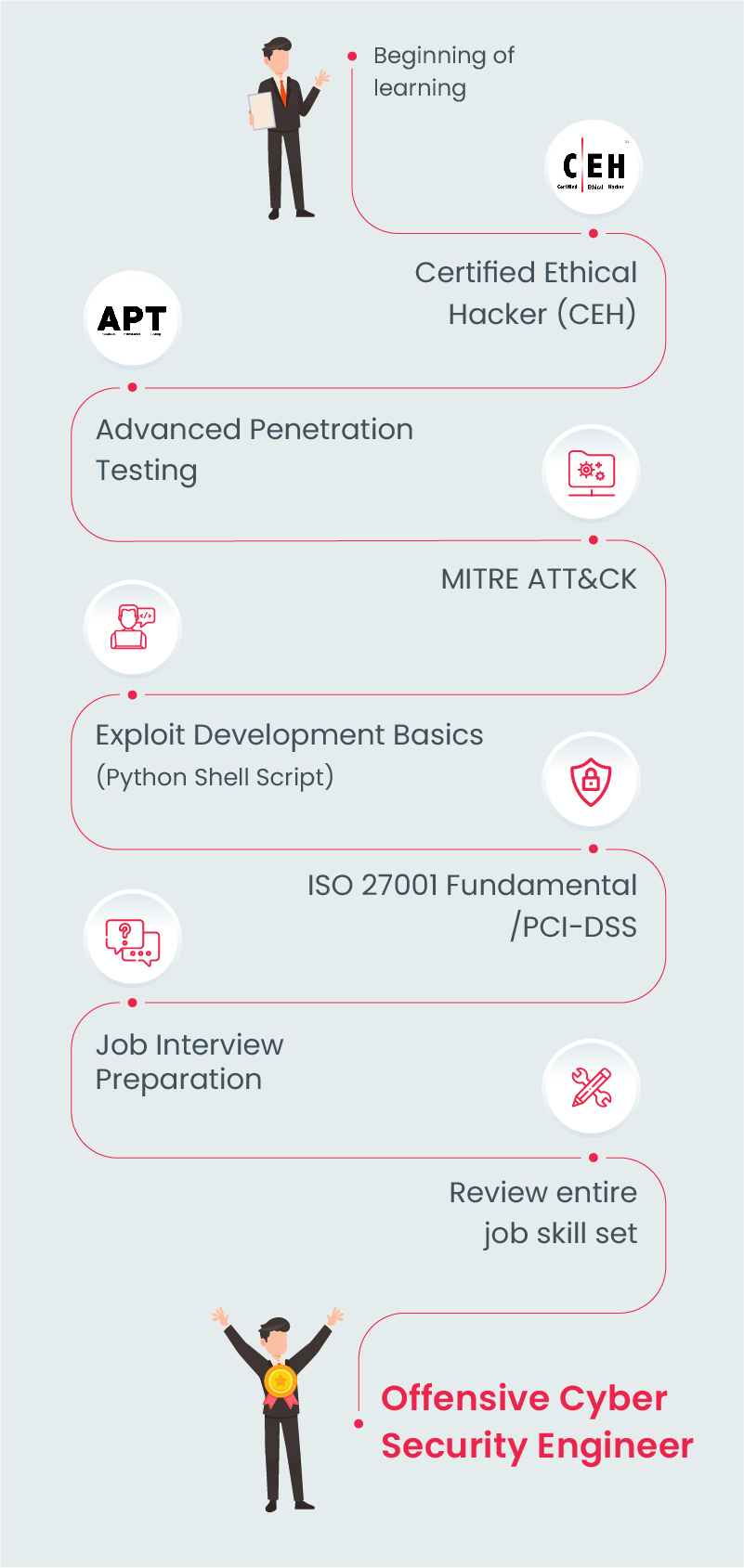
Offensive Cyber Security Engineer (OCSE) Certification Training
An Introduction to Offensive Cybersecurity and Red Team Certification
PPT Offensive Cyber Security Engineer Training PowerPoint
Certificate in Offensive Cyber Security
Offensive Cyber Security Engineer Training Program OCSE Training
Diploma in Offensive Cyber Security
Offensive Cyber Security Engineer Certification Training Cyber
As A Customized Course Registered As Part Of Ghabash's Personal Intellectual Property, It Provides An Unparalleled Learning Experience That Is Not Available Elsewhere.
Learn How To Conduct Ethical Hacking And Penetration Testing To Identify Vulnerabilities.
Which Provides Foundational Knowledge In Cybersecurity.
San Francisco — The Senior Director For Cyber At The White House’s National Security Council Told An Audience Thursday That He Wants To “Destigmatize” Offensive Cyber.
Related Post: